August, time for Hacker summer camp in the city of Las Vegas. In a space of 2 weeks, BSidesLV, Blackhat and DEFCON will grace this city. In Las Vegas, I had the pleasure of meeting the CIO of Las Vegas, Michael Sherwood. I really don’t envy his job especially when you have the world’s best hackers descending on your city and everything with a network stack becomes a target. True to the sayings of Las Vegas, Mr. Sherwood’s calling card is a chip off the block.
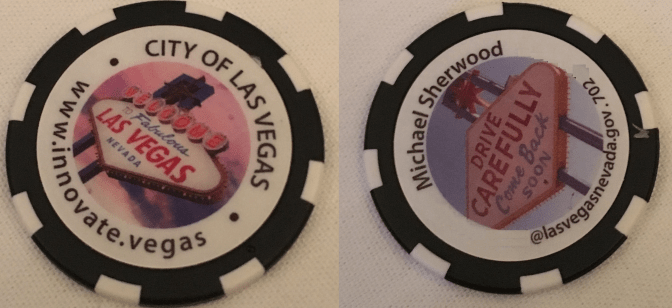
CIO Sherwood took a risk on Artificial Intelligence as an early adopter to help defend his city’s infrastructure from attacks. I think his foresight is paying off. Every year around July and August, wifi, cell towers, ATMs, and slot machines all go a little sideways. 2018 is no different.
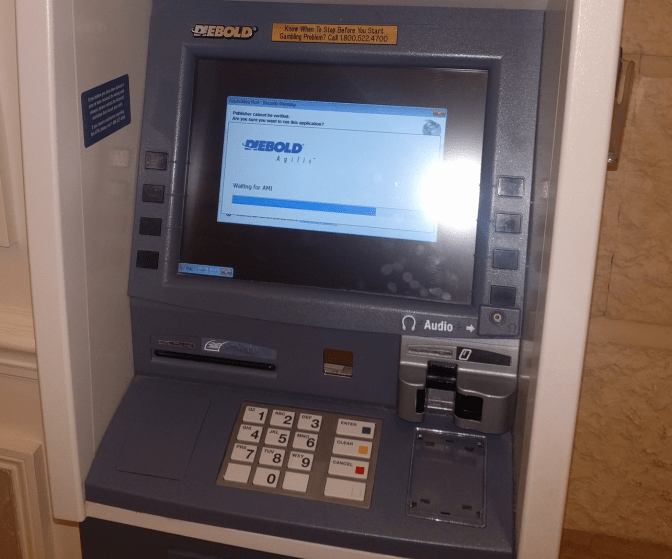
(Photo credit – http://www.mashable.com)
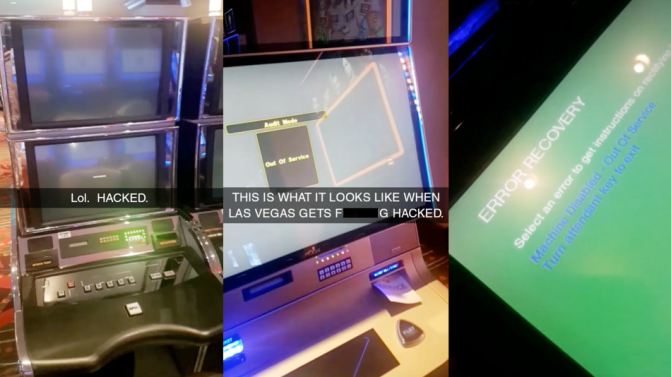
And to be fair, I too have taken a few shots at the casino wifi with great success. That said the great city of Las Vegas were the hosts and hackers made it their playground yet the city continues to function. Major kudos to Mr. Sherwood and the City of Las Vegas blue team for keeping the lights on.
Blackhat USA 2018
Similar to every year, Blackhat is hosted at Mandalay Bay. I spend most of the time meeting with my vendors and hope to return home with new tech for my company. Of the many vendors, the following, Cisco, Crowdstrike, Trendmicro, DarkTrace, Cylance, Nominet, Splunk, Microsoft, Okta, Rapid7, and Exabeam all had meetings with me and showcased their very best.
After the meetings with what little time I had left I attended as many Briefings as I could. The most notable one was given by Israeli researcher Mordechai Guri about “Jumping the Air Gap”. The attacks are a bit of something that come out of a James Bond movie.
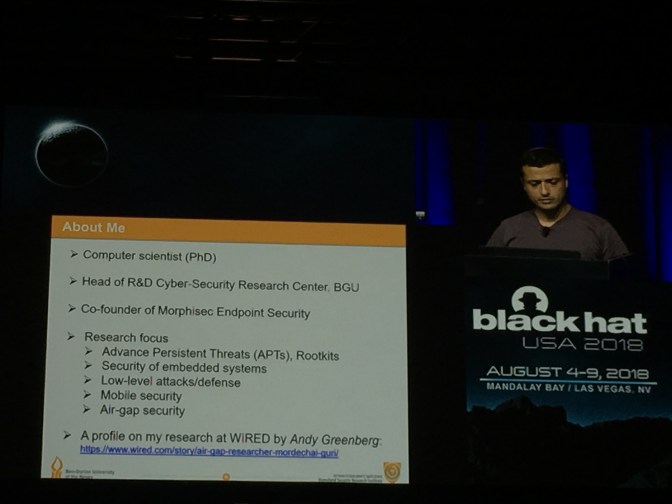
His presentation showcased 7 vectors of attack into an air gapped industrial network. USB is the most well known attack, the others are less known and at a much higher level of attacker skill and sophistication.
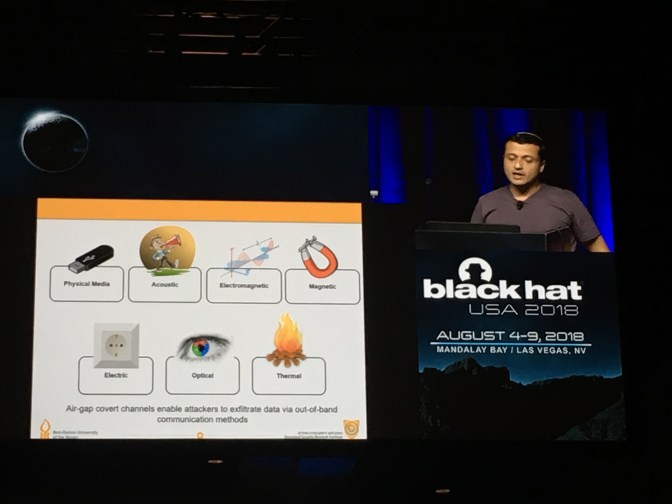
As a company that operates PLC and SCADA systems, these attacks are extremely relevant. We have air gapped networks that we protect due to its sensitive nature. Mr. Guri’s presentation was definitely an eye-opener.
The second most impactful presentation, in my opinion, was by Cisco engineers, Alfonso Garcia Alguacil and Alejo Murillo Moya about TLS 1.3. Why this is so impactful is that TLS 1.3 (RFC8446) is brand new, released August 10, 2018. It will govern secure communications in everyday life from banking to vpns to voip to websites. For me, if you can’t secure the TLS transmission, there is nothing safe on the internet.
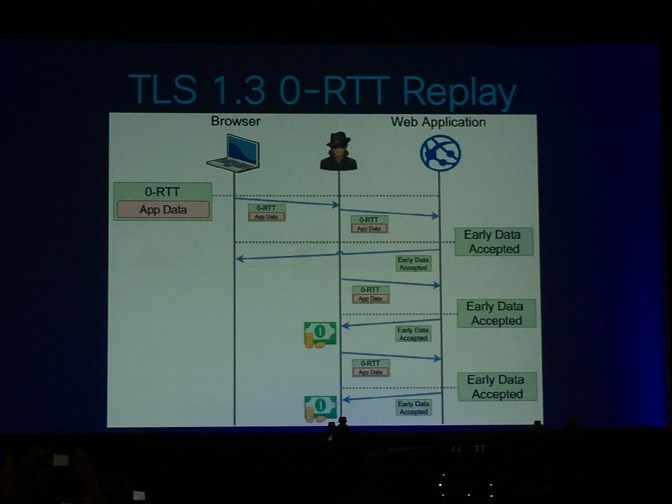
TLS 1.3 has a vector of attack that a bad actor can exploit because of the backwards compatibility of 0-RTT. Not sure why 0-RTT was included in TLS 1.3 personally it should have been deprecated back in TLS 1.2 and force all new applications to use only TLS1.3. Luckily, there are ways to mitigate this risk and developers of applications need to learn from this presentation and disable 0-RTT from practice as well write code that is resilient to replay attacks.
Aside from the briefings, I also signed up for the KALI Dojo training. As a security practitioner, I wanted to learn from the best and see if I was doing things correctly. By the end of the workshop, I won myself the KALI USB for being speedy. (NB: Offensive Security has the best motto “TRY HARDER!”)
All in all, Blackhat is a vendor-centric conference. The customer appreciation parties after the business hall has closed is definitely impressive as vendor thank their customers for their loyalty to product and brand.
The vendor parties usually signal the end of Blackhat and the beginning of DEFCON! Time for the hacker in me to play.
Next post: DEFCON 26






