
DEFCON is my once a year pilgrimage to spend a lot of time at the hacking villages and workshops learning new skills and attacks from world renown hackers and the attack tool writers themselves. This year I was lucky enough to not have to deal with LineCon to get a badge. I had arranged via Blackhat to get a DEFCON badge and I say this maybe one of the best reason to have a Blackhat admission… 🙂

A number of new tools that I would like to focus on as I found them quite useful.
EAPHAMMER (not new but great for WPA2-EAP hacking) by Gabriel Ryan

s0lst1c3’s EAPHammer is a great red teaming tool used to obtain the WPA2 Enterprise RADIUS credentials. There are 2 other options to harvest credentials via a web portal or captive portal where you force users to authenticate.
SILENT BRIDGE by Gabriel Ryan
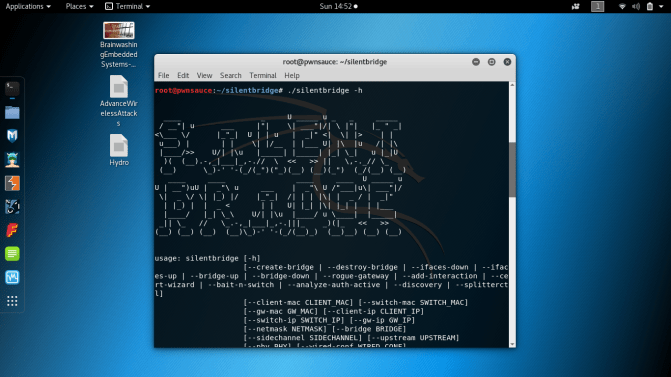
s0lst1c3’s newest tool Silent Bridge allows you to bypass Port based security. MACSec is used by most corporate defenders to control physical access to the network. In order to be successful with Silent Bridge, a rogue device must be inserted into the network without triggering MACSec. A good rogue device would need to have a transparent interface and for the POC there were 2 rogue devices built. First rogue device is a pure bridge device for use in the classic bypass attack. The second rogue device was a mechanical switch that involved the use of a solenoid to switch physical interfaces. This switching is needed to prevent the monitoring packets from spilling into the network, triggering MACSec. Silent Bridge toolkit will allow the attacker to bypass 802.1x-2004 and 802.1x-2010.
TRACKERJACKER by Caleb Madrigal
![]()
Caleb’s Trackerjacker is a tool pretty much made to work with EAPHammer or Hashcat-PMKID. As a Pentester or Red team, if you have ever needed to know what wireless networks are around you or what devices are connected to the access point or track a person based on his/her MAC. If you are a network admin, Trackerjacker can help you assess bandwidth use or see if an access point is being saturated.
SOCIAL MAPPER by Jacob Wilkin
Jacob’s SocialMapper is a very interesting (abet creepy) tool. It uses facial recognition to map which social media platforms a user is currently a member of. It works by first supplying the first and last name and a photo or supplying a social media URL. It will then use the photo with the name and search the following social media sites, LinkedIn, Facebook, Twitter, GooglePlus, Instagram, VKontakte, Weibo, Douban for a user account. I used it to do a check on myself, submitting my name with my photo. It found my facebook account but a bug prevented it searching Google and twitter. Jacob is currently fixing those issues.
Talks that I attended that I found most interesting
De-anonymizing Programmers from Source Code and Binaries by Rachel Greenstadt (Drexel University) and Aylin Caliskan (George Washington University)
My Voice is my passport by delta zero (Salesforce) and Azeem Aqil (Salesforce)
barcOwned—Popping shells with your cereal box by Michael West (Cyberark) and Colin Campbell
Exploiting Active Directory Administrator Insecurities by Sean Metcalf (Trimarc)
I’ll See Your Missile and Raise You A MIRV: An overview of the Genesis Scripting Engine by Alex Levinson and Dan Borges
Bypassing Port-Security In 2018: Defeating MacSEC and 802.1x-2010 by Gabriel Ryan (Digital Silence)
GOD MODE UNLOCKED: Hardware Backdoors in [redacted] x86 CPUs by Chris Domas
NSA talks cybersecurity by Rob Joyce (NSA)
Workshops – Advanced Threat Hunting with Splunk
I attended the 4 hour workshop lead by Splunk and it was very good from a blue team perspective. I also got to understand the huge amount of logging that Splunk can ingest. I will be taking this knowledge and bringing it back home to my corporation to train our staff. This was a very good workshop. Too bad it was only 4 hours long.
DEFCON Controversy
DEFCON 26 began with controversy, as privacy experts became victims of new security policies implemented after the Mandalay Bay shootings.
The Oct 1 tragedy has led to controversial new security measures at Las Vegas hotels, one of which includes room checks by hotel security. Throughout the conference, held at Caesars’ Palace, there were multiple attendee reports of illegal entries and seizures from Caesar’s Palace security. Seizures allegedly included electronic equipment, lock picks, U2F tokens and soldering irons. While improved security measures were undoubtedly needed, and included a policy of entering rooms that turned down maid services, security staff responded disrespectfully and escalated actions with impunity without proper oversight.
One such affected expert was Katie Moussouris (a world renowned security researcher that has testified in front of the U.S. Senate Subcommittee on Consumer Protection, Product Safety, Insurance, and Data Security). Here’s her reaction on Twitter:
I was lucky to avoid the searches, but this situation is certainly disturbing, from a security policy and privacy perspective. I hope the security policies and their implementation is reviewed and revamped, to balance public safety appropriately with the protection of the individual’s rights and privacy.
That said, this maybe one of the reasons why DEFCON 27 will not be at Caesar’s Palace. I am speculating here, and will wait for after the conference to hear the official reasoning.
Canadian Party
I did a little networking and met up with the Canadian contingent from TASK and it was a great time with other Canadians. This is largest group from Canada compared to previous years and I am glad there is an uptick in Canadian cyber experts.
Monero Party
I stopped by the Monero party and hung out with some of the best crypto minds in the digital currency world. These guys are genius level mathematicians. I think crypto currency is here to stay given the experts working in this field.

DEFCON – Juno Reactor!
On the last night Juno Reactor performed for DEFCON and it was amazing. Hackers need time to relax too and this was needed to help unwind before the packing and flights home the next day. I almost didn’t make it to Juno Reactor as I was working late on cracking some crypto thankfully it was solved in time.
The next day is packing day and the mad rush to the airport to return home. I will be back next year to learn from the best, to compete with the best and to raise the standard to cybersecurity for all. I will leave you with some photos from the conference and see you next year at Blackhat/DEFCON 2019.






































































