One of the largest cybersecurity conferences DEFCON, this year had a Voting Machine hacking village for the first time. An open invitation for attendees to get hands-on experience hacking a slew of voting machines, WINVote, Diebold, Sequoia AVC Edge, ES&S iVotronic and AccuVote TSX. So challenge accepted!!! Friday came about and I made my way down to the Voting machine hacking village armed with the idea that I am helping flush out the bugs in these devices and securing the future of electronic voting.
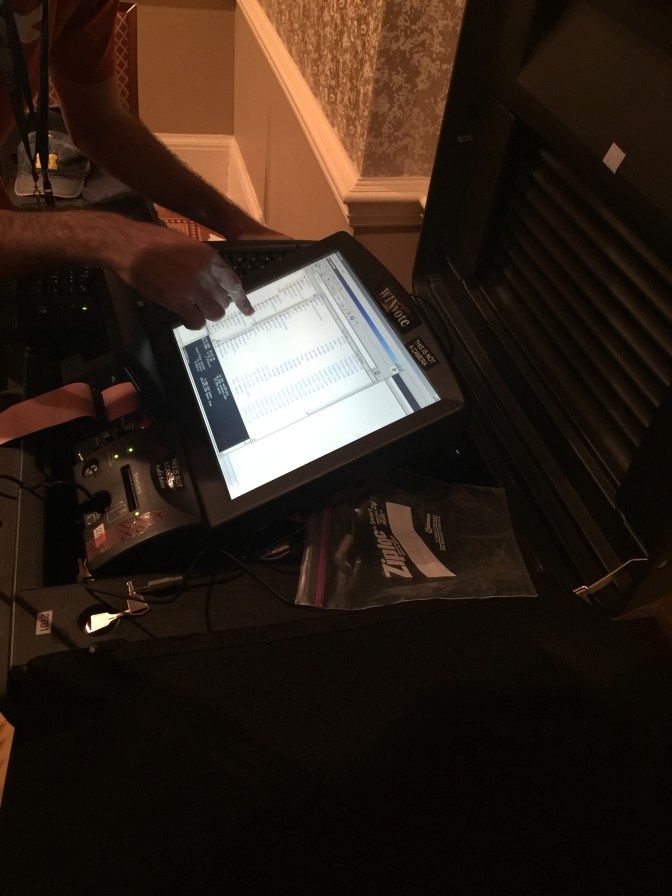
When I got there, the WinVote machine had already been playing “Never Gonna Give You Up” and the next group was attempting to install VLC on it (It was successful if you are curious).
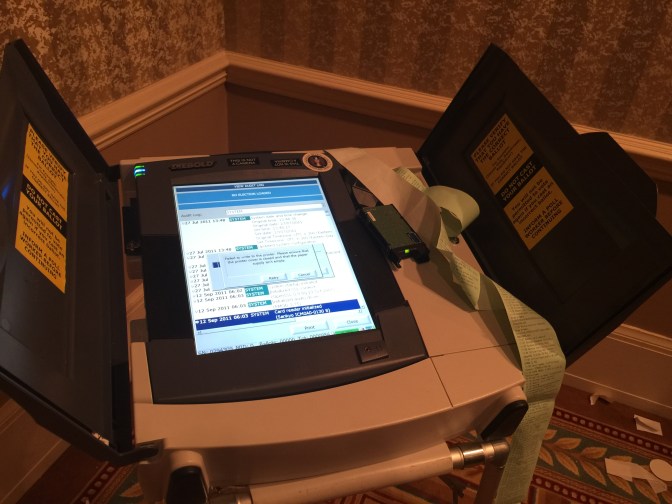
So I moved on to the other machines, so next up the TSX which was in the process of being completely destroyed as the Epson printer was spitting out paper and errors were overlayed on-screen. Needless to say, I feel a tad bit too late to the party… but wait… the Diebold Expresspoll 5000 was still being worked on and so I joined the merry band of security techs.
About the Diebold Expresspoll 5000
The Diebold Expresspoll 5000 is a voter registration machine. Essentially, it is a voter check-in device that houses a voter database and check to see if that voter is voting in the correct place and validate their eligibility to vote.
On power up, the Diebold seems to be looking for an OS image from the CF. “Download Image from CF Card to RAM. OK good to know and if you have any cisco experience you will know it is pretty normal to store a .bin file on CF which is essentially your operating system. Once loaded, the ExpressPoll software will require a consolidation number plus username and password which is shockingly hardcoded username = 1 and password = 1111.
With ExpressPoll launched we need to create a voter registy and a new poll so next we look at the storage system and see what files are there to play with.
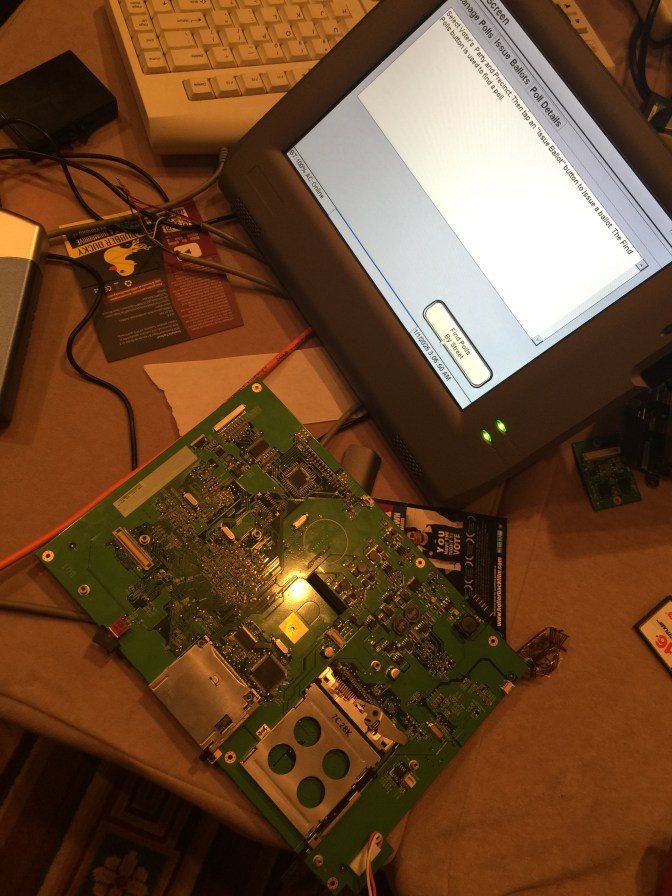
It took some time opening up a bricked Diebold, we can see 2 storage areas on the top under plastic covers: PCMCIA and CF.
At a quick glance the Diebold Expresspoll 5000 runs:
Running an Intel ARM CPU
OS image is booted from CF (128MB)
Storage is PCMCIA (32MB)
USB ports and Ethernet are removable

This further confirms the CF storage during the boot up sequence. Next finding out what is on these storage cards.
CF card contains a NK.bin file, a PollData.db3 file and a couple of .xml error logs. There is no encryption on any of the files retrieved. Someone told me the PollData.db3 it is a SQLite database. Strangely the PCMCIA card also has a PollData.db3 file and a number of other .db3 files.
I’m guessing CF is OS storage and PCMCIA is DB storage and misc.
Swapping files from CF to PCMCIA and vice versa will cause the Diebold to stop working… so make sure the NK.bin file is on the CF.
Opening the db3 file, you get the following database from the voters table:
0 – voterId
1 – precinctId
2 – name
.
.
.
The important PII is in fields 13-21
13 – ssnLast4
14 – driversLicense
15 – affidavidNumber
16 – houseNumber
17 – houseFraction
18 – streetName
19 – apartmentNumber
20 – city
21 – zip
So here is the voter registration, and I’m surprised that I can modify the fields and then transfer the edited database back into the device and it would accept the values.
Oh and by the way, there is no data encryption… fml!
The underside of the device reveals 2 USB ports and an ethernet port which could also be used as an attack vector. The network port seems open to port 80 HTTPD. I believe this might be for the handheld scanner but I didn’t have time to test it.
Plugging in a mouse or keyboard gives you touchscreen access, plug and play is suspected which would be another attack vector.
Illuminating the Vulnerabilities
Pretty much if you have physical access to the Diebold, you can hack and steal from it.
There should be a hardware alarm to alert when the plastic covers are removed from the top.
The storage devices should be encrypted to prevent someone stealing the voter database or manipulating the database. Once you have access to the voter database, it is pretty much game-over. You can steal the PII of voters, manipulate or create a custom the voter registrar and generate “fake” votes. This can all easily be done with just a little pre-planning, physical access to the device and a PCMCIA card.
My neighbours were experimenting with custom firmware and seem to be having a lot of success. So I would say that is definitely an area of vulnerability. If a custom firmware can be injected, you would have full control of the device. Highly recommend the firmware be signed at the very least so you can’t replace the CF card with your custom firmware.
Locking down USB – I noticed the usb ports are hardware detachable. I would recommend they remove the USB and ethernet ports if they are not used. If not, have some logic in place to lock down the usb ports to only approved devices.
